










Rapidsoft systems provides complete solution for homeland security for CBRN detection system in partnership with several US security companies. We are official worldwide distributor of world's most advanced CBRN systems.
The system consists of several systems
1. Defentect CBRN System
2. Video Analytics Solutions
3. Advanced Fibre Optics Perimeter Protection System
All these products are backed by security experts on the homeland security.

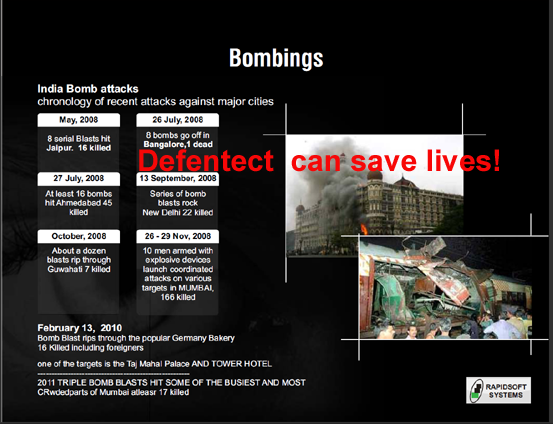
Our advanced Defentect Threat Awareness Solution can provide security over the complete gamut of threats:
The unique core of the Defentect Threat Awareness Solution is Defentects DM3 software. DM3 gathers data from virtually any sensor, motion detector, video analytics enabled camera, which can live on a data network; then, using its algorithms, DM3 seeks and identifies anomalies in the data and forwards that new information to an unlimited number of virtually any type of device which can receive a message--such as SMS, email, smartphones, voicemail, XML --and notifies those who should respond or be notified of the event, instantaneously and without human action required.
The Defentect Threat Awareness Solution, developed some time ago, is deployed within the United States, and is a proven threat-awareness solution for nuclear power plants, hospitals, and other high-value targets. Originally designed for first-responders in a high threat environment, and based on a distributed network of sensors, the system protects and defends by sending real-time notifications to multiple pre-designated security command centers when the presence of a threat is detected. The integrated Defentect DM3 system enables customers to add other threat event detection capabilities to their security systems and to easily customize highly configurable alerts when any anomaly is detected and change the notification list. Administrators can designate alerts to be triggered to cell phones, smart-phones, pagers, PDAs and other devices through text messages, calls, or email.
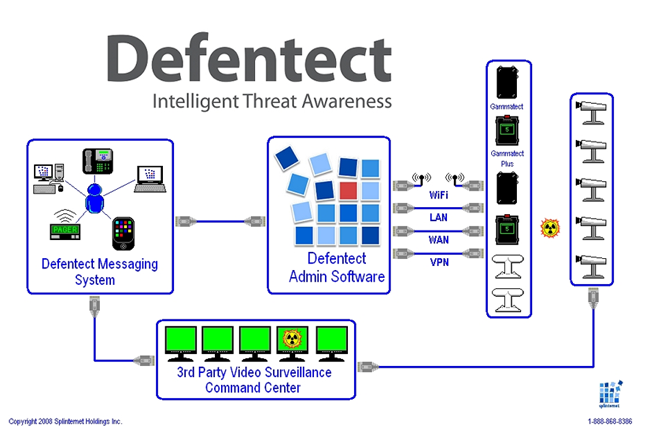
Defentect combines passive surveillance and active alerts when a threat is detected. No special training or added security staff is required. DM3 is designed to overlay onto existing surveillance infrastructure. DM3 is easily integrated with the full complement of data-based security systems, from stand-alone to enterprise-level solutions. Threat-level alerts are generated to multiple user accounts with various privileges.
Communication features of DM3 provide the ability to receive and process data over a network from sensors to an incident command center as well as to PDAs, cellphone, smartphones, pagers, or computers. DM3 is networked using IP and managed over the Web. DM3s proprietary algorithms analyze data and alert multiple authorities to a security threat, removing the local on-scene personnels need to interpret the data.
In addition to the hardware, the software, and the installation of the hardware and software at any location, the Defentect Threat Awareness Solution can provide the specialized training, and personnel, needed from experts with experience in Iraq and Afghanistan.
Please contact us for more details on pricing and other custom features. We offer several pricing options - licensing and usage based pricings. Customization changes based on specific customer requirements can be done. Integration with end user systems is provided.